👩💻Bug Bounty Tips, Desync Attacks, SSRF, SQL Injection, Vulnerabilities in CPU, RCE, and much more…
An overlooked parameter leads to a critical SSRF in Dropbox bug bounty.
Hey 👋
Welcome to the #IWWeekly20 - the Monday newsletter that brings the best in Infosec straight to your inbox.
For those of you who are from India, Happy 75th Independence Day 🤗🥳
Remember, don't treat this day like a holiday! Work religiously on your Infosec goals. Because work is the only thing that can write your ticket to freedom ✈️
Coming back to topic, here are our top picks for this week: 5 articles, 4 Threads, 3 videos, 2 Github repos and tools, 1 job alert to help you maximize the benefit from this newsletter and take a massive jump ahead in your career.
Excited? Let’s dive in👇
📝 5 Infosec Articles
#1 Learn how to combine cross-domain requests with server flaws to poison browser connection pools, install backdoors, and release desync worms through browser powered desync attacks. by James Kettle.
#2 Enhancing the subdomain enumeration by including a special DNS node that is often ignored - ENTs and NOERROR.
#3 Bypassing authentication when accessing the same endpoint (mboximport) used by CVE-2022-27925 in Zimbra Collaboration Suite (ZCS) email servers, making the vulnerability significantly more critical in severity.
#4 @Vimanari shares how they found an unauthenticated Jenkins dashboard that belonged to a Fortune 500 company from Shodan resulting in RCE.
#5 The quantum state of Linux kernel garbage collection CVE-2021-0920 (Part I) is a deep dive into an in-the-wild Android exploit where a surveillance vendor named Wintego was able to remotely root Samsung devices.
🧵4 Trending Threads
#1 Check out @rez0’s thread regarding his the technical takeaways from the h1-702 event.
#2 Missed some bug bounty tips from Intigrity’s #bugbountytips threads? @Nithin R shares his 5 personal favourite tips by Intigriti.
#3 @Abhishek Meena’s new thread can be valuable to you if searching for some free labs to upskill your pentest/ctf skills.
#4 Blockchain & smart contract security - distinguishing EOA and smart contracts securely by @Shashank.
📽️ 3 Insightful Videos
#1 Gregxsunday goes over an overlooked parameter that leads to a critical SSRF in Dropbox bug bounty.
#2 LiveOverflow explains concepts like CPU caching and out-of-order execution and how these introduce an array of vulnerabilities in CPUs.
#3 Code Review vs. Dynamic Testing explained with Minecraft by LiveOverflow.
⚒️2 Github repositories & Tools
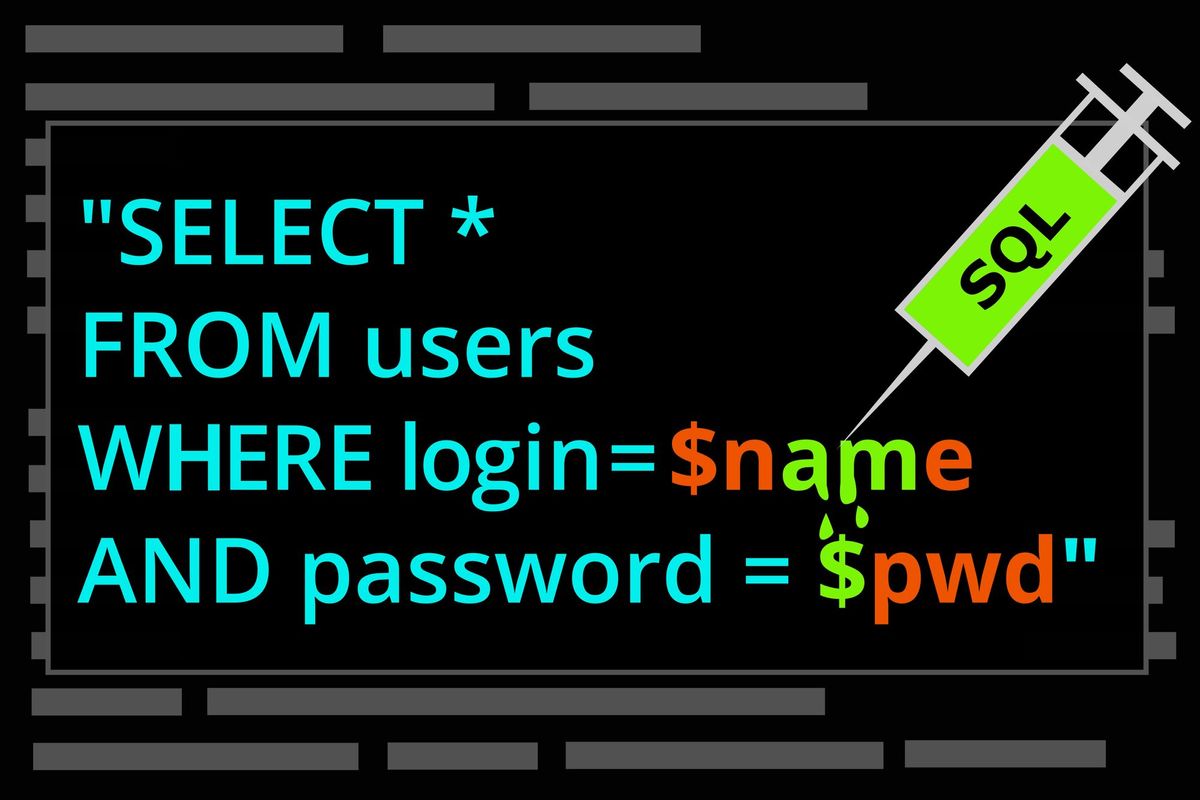
#1 Logsensor is a powerful tool to discover login panels and scan them for SQL injection by @Mr_Robert20.
#2 Medusa is a framework that automates processes and techniques practiced during the dynamic analysis of Android Applications by @Ch0pin.
💰1 Job alert
#1 A remote job opening for application security engineer, appsec reviews and assessments at NETFLIX.
💸Advertise with us💸
We are looking to partner with amazing infosec, pen testing, and ethical hacking teams, brands, and companies from all over the world. If this sounds like you, click here to partner with us.
That’s all for this week. Hope you enjoyed these incredible finds and learned something new from today’s newsletter.
Before we say bye…
If you found this newsletter interesting, and know other people who would too, we'd really appreciate if you could forward it to them 📨
If you have questions, comments, or feedback, just reply to this email or let us know on Twitter @InfoSecComm.
See you again next week.
Lots of love
Editorial team,
This newsletter has been created in collaboration with our amazing ambassadors.
Resource contribution by: Bimal K. Sahoo, Nikhil Memane, Siddharth, Vinay Kumar, Pramod Kumar Pradhan, Nithin R, Hardik Singh, and Bhavesh Harmalkar.
Newsletter formatting by: Nithin R, Vinay Kumar, Hardik Singh and Siddharth.
If you wish to join our Ambassadors channel and contribute to the newsletter, send us a DM on Twitter with your discord username.
